SSH Connection Manager: Tengingarstjóri
Tengingarstjóri, tg for short, is a Python TUI based SSH connection manager that integrates seamlessly with your existing SSH configuration.
Add new hosts with tg add
$ tg add -n "test-proxy" -h "internal.example.com" -u "admin" \
--proxy-jump "bastion.example.com" \
--local-forward "3306:localhost:3306" \
--notes "Test connection with proxy and tunnel
List hosts with the tg list command
Supports table, compact and json output formats.
$ tg list -f compact
SSH Connections:
1. deep-internal - root@172.16.5.10:22
2. test-proxy - admin@internal.example.com:3306
3. callisto - ryan@192.168.86.56:3356
$ tg list -f json
{
"connections": [
{
"name": "deep-internal",
"host": "172.16.5.10",
"user": "root",
"port": 22,
"identity_file": "/Users/ryan/.ssh/id_ed25519"
},
{
"name": "test-proxy",
"host": "internal.example.com",
"user": "admin",
"port": 3306,
"identity_file": "/Users/ryan/.ssh/id_ed25519"
},
{
"name": "callisto",
"host": "192.168.86.56",
"user": "ryan",
"port": 3356,
"identity_file": "/Users/ryan/.ssh/id_ed25519"
}
],
"total_count": 3,
"detailed": false
}
Architecture
Rather than modifying your main SSH config directly, Tengingarstjóri will:
- Create a managed config file:
~/.ssh/config.tengingarstjori - Add a single line to main config to include our new file:
Include ~/.ssh/config.tengingarstjori - Manage connections separately: All additions/changes go to the managed file
- Preserve your existing SSH setup: Your existing SSH config remains untouched
Yeah, but the name?
Tengingarstjóri is Icelandic for "Connection Manager". If I can't think of a good name for a new project, I default to trying to find an Icelandic alternative.
kylfuskofu: Site scraper/aggregator with Discord Webhook
This application collects random websites from multiple sources (indieblog.page, hackernews, 512kb.club), stores them in a SQLite database, and (optionally) syncs the database with IBM Cloud Object Storage. It also sends notifications to a Discord webhook with clickable links to the discovered sites.
But why?
Fair question. I am building this little tool for a few reasons:
- I learn best when I have a problem to solve and I am trying to learn more python in 2025. Two birds, one stone.
- I love the concept of sites like https://512kb.club/ and https://indieblog.page, but visiting the site and clicking the Random Site button 20-30 times a day is annoying.
- While not all sites are going to be up my alley or even in my native language, I want a way to discover more people and information outside of the traditional social media sites.
- I want more data coming into my RSS reader and I am looking for ways to aggregate content and provide myself with more tailored feeds.
Use Python and Certbot for custom domain mapping for IBM Cloud Code Engine
This script automates the process of mapping a custom domain to an IBM Cloud Code Engine application using Certbot and the multi-dns plugin to generate a TLS certificate and store it as a Code Engine Secret. Code is available on Github
Github Action for IBM Cloud Code Engine
This Github Action allows you to deploy or update Code Engine workloads
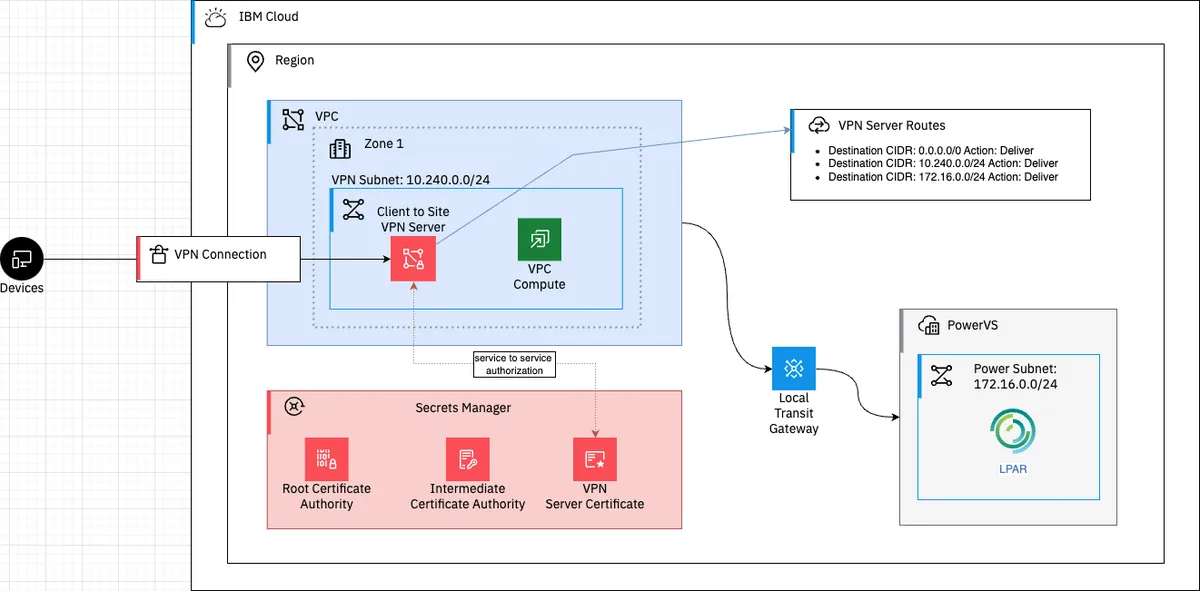
Connect on-prem to VPC and PowerVS using Client to Site VPN.
Use Terraform to spin up an IBM Cloud Client to Site VPC VPN and Transit Gateway for extending on-prem connectivity into PowerVS. Repository